Let’s discuss how Block Webshell and Creation of Suspicious Executions on Server using Intune ASR Rules. Webshell is a small program or script that a hacker can install on a server. Once it’s there, that’s it hacker can control the server remotely.
Once the webshell is installed, attackers can do this execute the commandmanipulate files, steal sensitive data, and even spread ransomware. Hosting servers web application is a prime target for webshell attacks because it is frequently hit Internet and may have vulnerabilities that can be exploited by attackers.
One of the highlights of our post Application Control for Businessa powerful Windows security solution that blocks unwanted applications and malware. By using IT policy rules combined with Microsoft’s AI-based application reputation technology, it ensures only trusted apps run on the device. This proactive approach prevents invalid software, reduces security risks, and helps organizations maintain a more secure and compliant computing environment.
This post explains how to block webshells and suspicious executable creations on the server using Intune ASR (Attack Surface Reduction) rule. By enforcing these rules, organizations can prevent attackers from running malicious scripts, installing without permission programor gain persistent access to the server.
Block Webshell and Creation of Suspicious Executions on Server using Intune ASR Rules
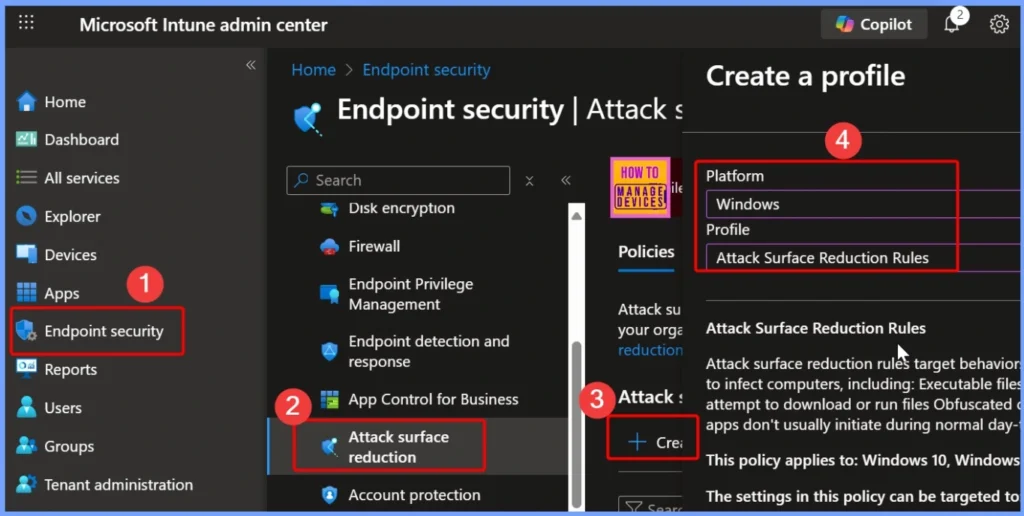
To block webshell and suspicious executable creation on the server using Intune ASR rules, first log in to Microsoft Intune Admin Portal with your credentials. Then navigate to Endpoint security > Attack surface reduction > Create a Policy to start configuring the necessary security settings.
- Benefits for Server Security
- Reduce risk of server compromise
- Prevents attackers from uploading web skin even if there are vulnerabilities
- Protect sensitive data from unauthorized access
- Maintaining service availability and uptime
- Limits internal lateral movement network
- Act as a proactive defense layer on the side firewalls, endpoint protection, and intrusion detection systems
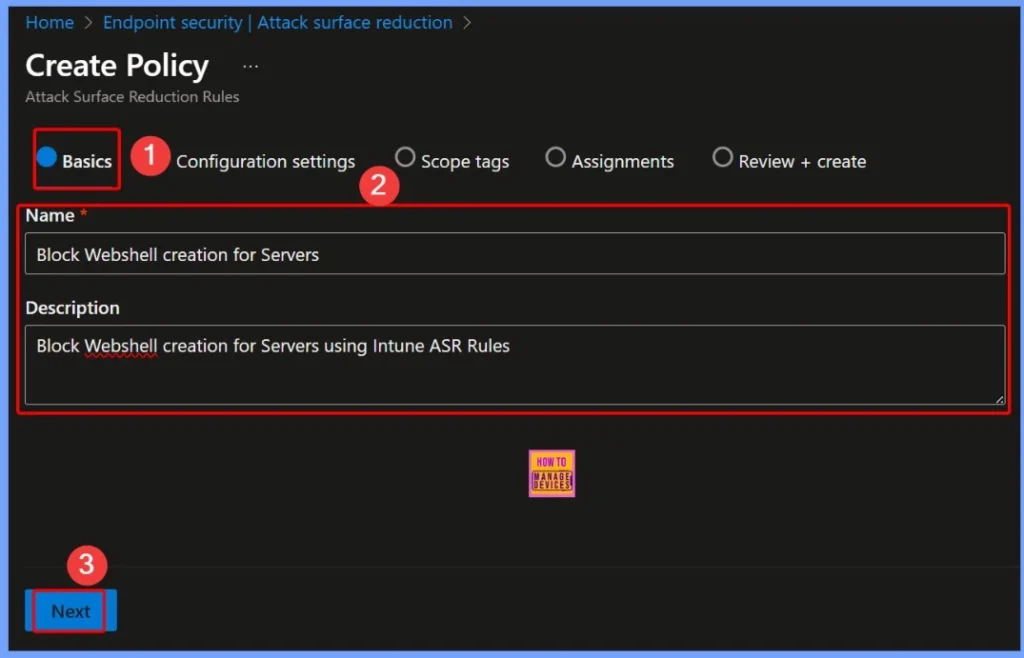
ASR Policy Basic Settings
In basic settings ASR policyYou need to provide important details like: Name: Block Webshell Creation for Server, Description: Block Webshell creation for server using Intune ASR rules. These details help identify the policy and clarify its purpose secure your server against malicious webshells.
| Policy Name | Information |
|---|---|
| Block Webshell Creation for Server | Block Webshell Creation for Server using Intune ASR rules |
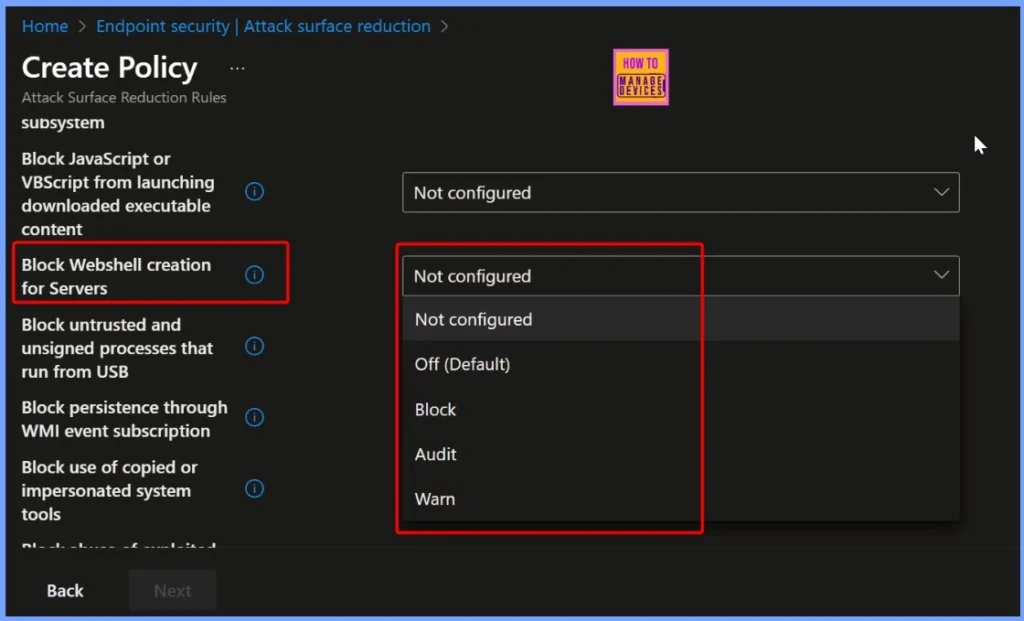
Default Setting to Block Webshell Creation
By default, the Block Webshell Creation for Server setting in Intune ASR rules is Not Configured. This means protection is inactive until an administrator explicitly enables and applies the policy, ensuring the server persists unprotected from webshell threats to configured rules.
| Block Webshell Creation for Server |
|---|
| Not Configured |
| Off (Default) |
| Block |
| Auditing |
| Warning |
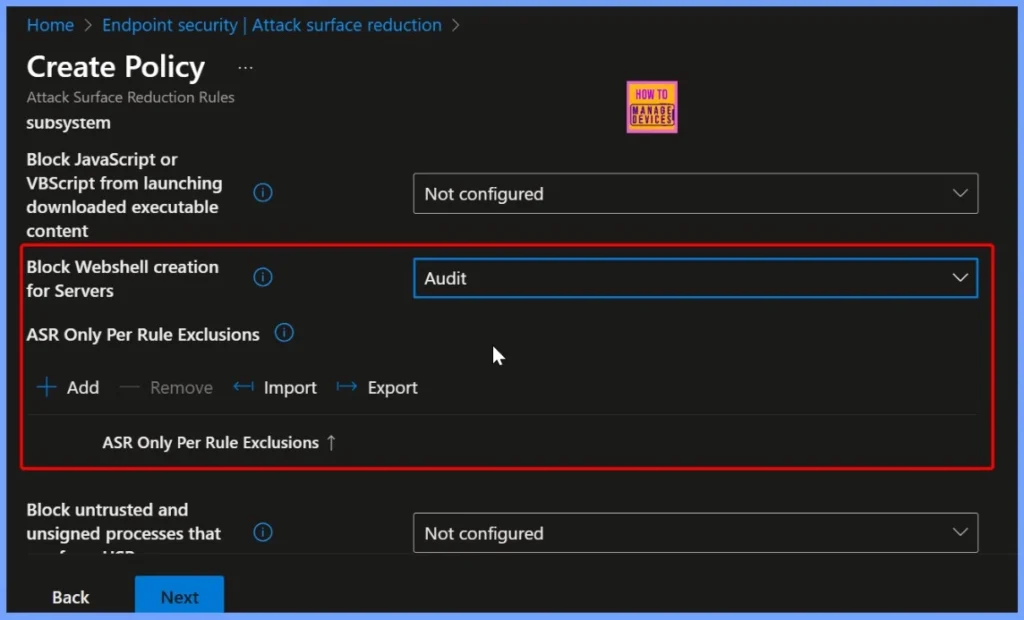
Webshell Creation Protection Enabled
Settings Block Webshell Creation for Server now activatedactively prevent webshell creation on your server. With this protection, the server will be protected protected oppose malicious script which could allow an attacker to gain unauthorized access or control.
| Block Webshell Creation for Server |
|---|
| Auditing |
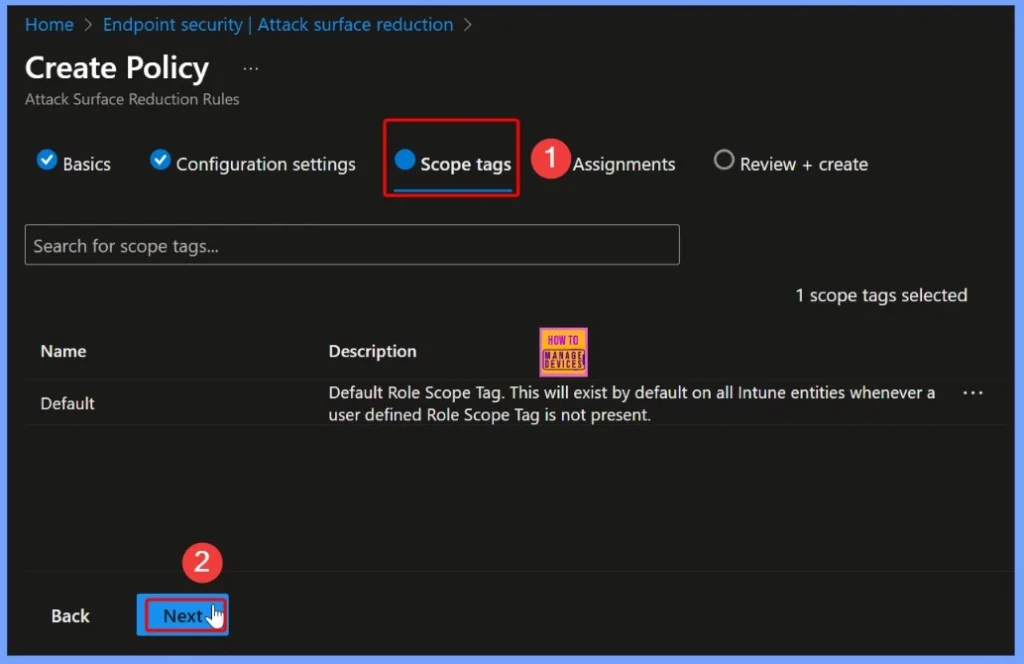
Webshell Build Protection Enabled – Coverage Tag
After enabling Webshell Creation Protection, you can set a scope tag to determine which groups or devices apply the policy. Coverage tags help IT administrators manage and target security policy efficiently across teams or organizational units, ensuring that only the intended server receives web skin protection.
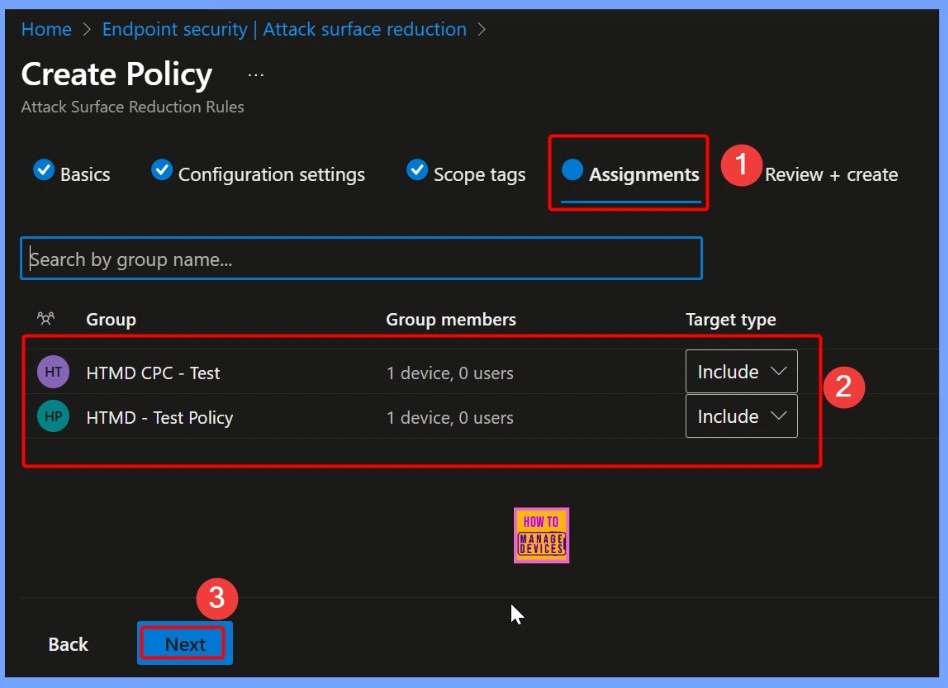
Understanding the Tasks Tab in Intune
That Assignment tab in Intune is where administrators determine which users, devices, or groups should apply policies. By configuring tasks, you can target security settingsapplication, or configuration to the right endpoint, ensuring only what is intended device or the user accepts the policy.
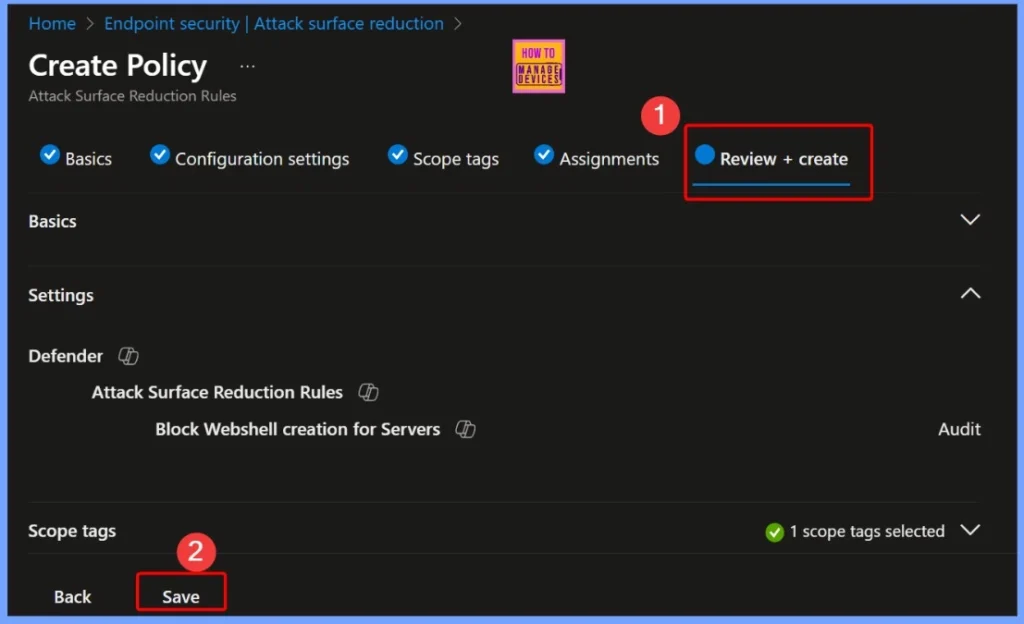
Verify All Policy Settings Before Deployment
That Review + Create step in Intune allows administrators to verify all policy settings before deployment. Here, you can double check configuration, coverage tags, and the task of making sure everything is correct. Once reviewed, you can click Make to apply policies, enable protections such as webshell blocking or other security measures on targeted devices.
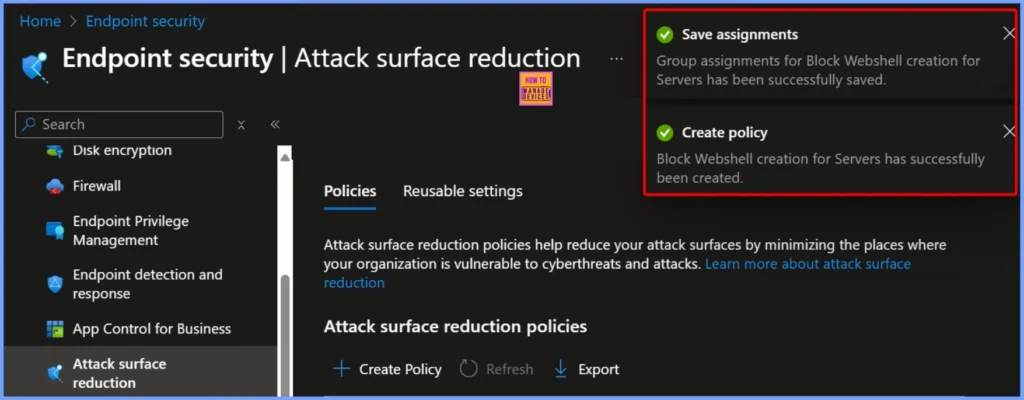
Notification of Determination and Policy Making
After configuring assignments, a announcement confirms that the group assignment for Webshell Block Creation for Server has been successful saved. After this, another notification shows that the policy has been successfully created, confirming that the webshell protection is now active and applied to the targeted server.
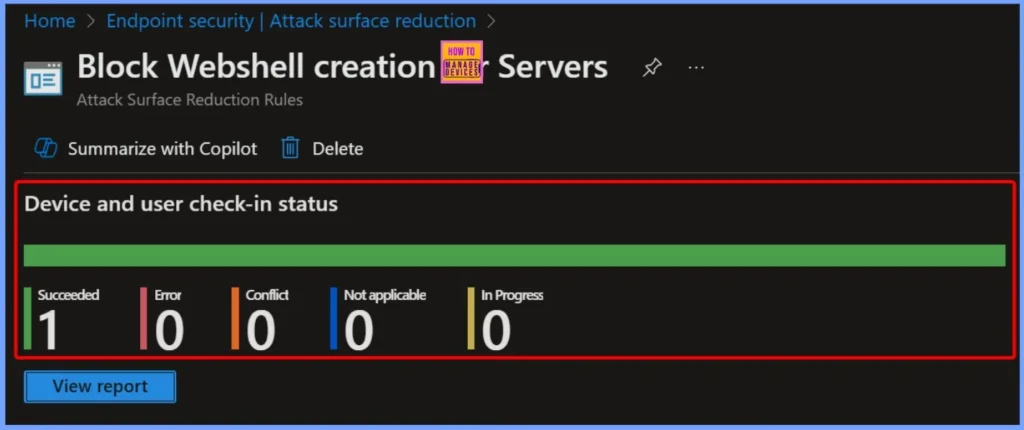
Device and User Check-in Status – Successful Deployment Status
Policy Block Webshell Creation for Server below Attack Surface Reduction the rule indicates successful deployment status. According to latest device and user check-in reports, 1 device successfulwith 0 conflicts, 0 not applicable, and 0 in progress, indicating that webshell protection is implemented and operating effectively.
Client Side Verification
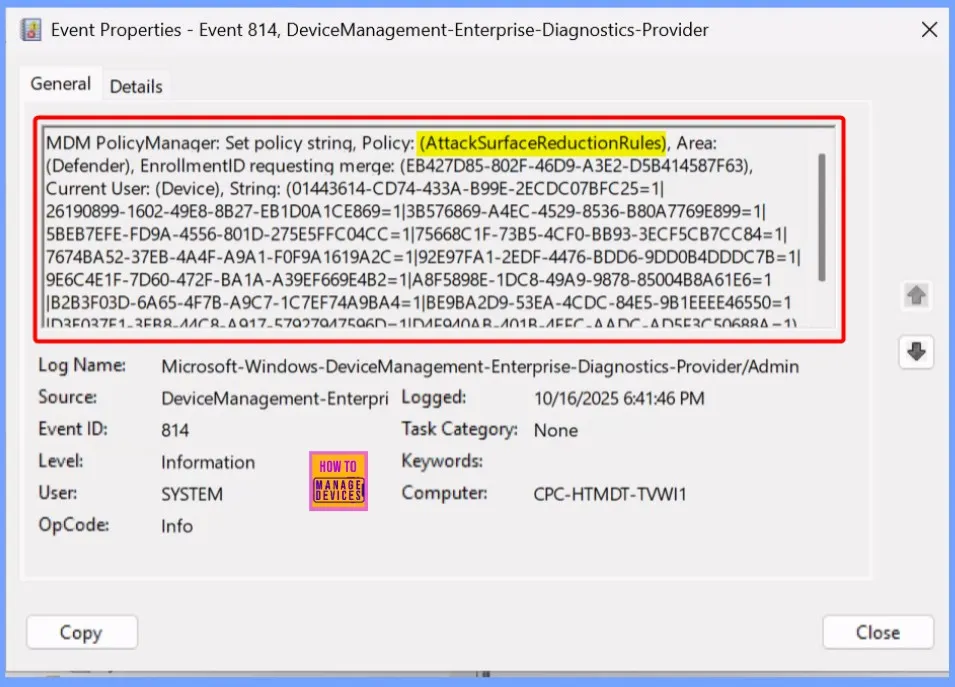
The “Block Webshell Creation for Server” rule helps you prevent the creation or execution of suspicious scripts on the server. It monitors file system activity and identify patterns commonly associated with webshells, such as the creation of files with executable extensions web directory or scripts that contain obfuscated code.
To confirm this, check Event log path – Application and Service Logs – Microsoft – Windows – Device Management-Enterprise-Diagnostics-Provider – Admin.
Need More Help or Have a Technical Question?
Join LinkedIn Page And Telegram Group to get step by step guides and latest news updates. Join us Meet Page to participate in User group meetings. Also, Join WhatsApp Community to get the latest news about Microsoft Technologies. We were there RepeatDhe as well
Author
Anoop C Nair has been a Microsoft MVP from 2015 onwards for 10 years in a row! He is a Workplace Solutions Architect with over 22+ years of experience in the Workplace technology space. He is also a Blogger, Speaker, and Local User Group Community leader. The main focus is on Device Management technologies such as SCCM and Intune. He writes about technologies like Intune, SCCM, Windows, Cloud PC, Windows, Entra, Microsoft Security, Career, etc.
Game Center
Game News
Review Film
Berita Olahraga
Lowongan Kerja
Berita Terkini
Berita Terbaru
Berita Teknologi
Seputar Teknologi
Berita Politik
Resep Masakan
Pendidikan
Berita Terkini
Berita Terkini
Berita Terkini
review anime
Gaming Center
Originally posted 2025-10-23 11:34:42.


