Important Points
- Introducing the dedicated AI pillar to strengthen the Zero Trust strategy
- Covers 700 security controls 116 logical groups and 33 functional swim lanes
- Scenario-based and decisive approach for faster execution
- Helps align securityIT, and business teams on the same goal
- Expand Zero Trust Principle across all pillars, including AI
Zero Trust Workshop 3.0 has been enhanced with a dedicated AI pillar, significantly expanding its scope and relevance. Now included 700 security controls organized in 116 logical groups and 33 functional swim lanes, offering a more structured systemd comprehensive approach to modern security challenges.
List of contents
Zero Trust Workshop 3.0 Updated with AI Pillar 700 Safety Controls in 116 Groups and 33 Functional Swimming Lanes
This workshop follows a scenario-based and prescriptive modelsenabling organizations to move efficiently from assessment to implementation. The workshop gives you real life situations not just a theory. For each situation, it also tells you what steps to take. So instead of just checking you current securityit helps you quickly iterate to actually fix and improve things.
| Area | Details |
|---|---|
| Stakeholder Alignment | Bringing together security, IT, and business teams to achieve common goals |
| Zero Trust Coverage | Implement Zero Trust principles across all pillars, including AI |
| Security Consistency | Ensure an integrated and consistent security posture across the environment |
| AI Scenario Exploration | Help teams understand real-world AI use cases and associated risks |
| Cross Product Integration | Connect multiple tools to reduce silos |
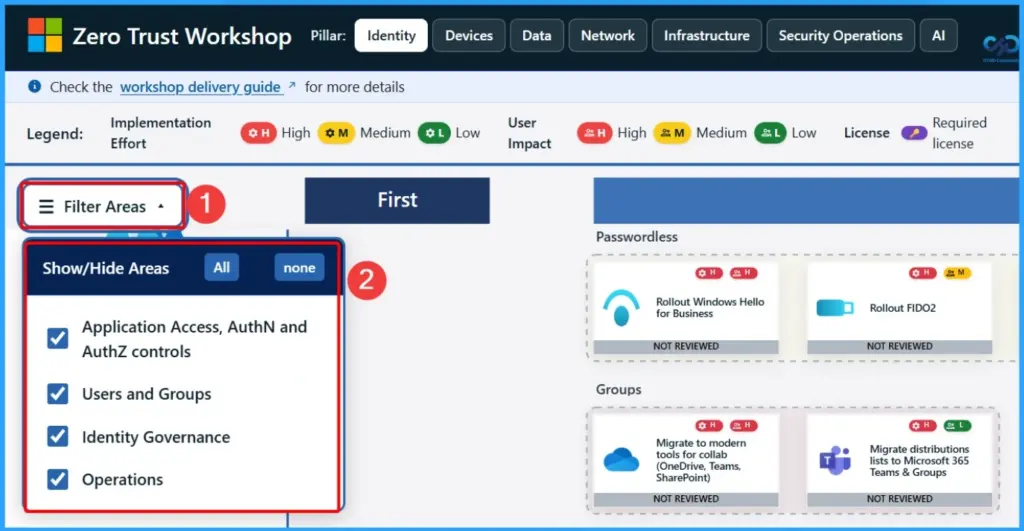
Filter Area in Zero Trust Workshop
At Zero Trust Workshop, you can use filter to focus on key security areas. Access Applications and AuthN/AuthZ controls ensure the right users access the right resources. Users and Groups helps manage identities, Identity Governance oversees policy and compliance, and Operations provides ongoing activities to keep your environment secure and well-managed.
| Show or Hide Areas |
|---|
| App Access, AuthN/AuthZ control |
| Users and Groups |
| Identity Governance |
| Identity Governance |
Need More Help or Have a Technical Question?
Join LinkedIn Page AndTelegram Group to get step by step guides and latest news updates. Join usMeeting Pageto participate in User group meetings. Also, join inWhatsApp Communityand itWhatsapp Channelto get the latest news about Microsoft Technologies. We were thereredditas well.

Author
Anoop C Nairis a Workplace Technology solutions architect with over 25 years of experience. Microsoft Certified Trainer. Microsoft MVP from 2015 onwards for 11+ years in a row! He is a blogger, Speaker, and Founder of the HTMD Community and HTMD Conference. The main focus is on Device Management technologies such as Intune, Windows, and Cloud PC. He writes about technologies such as Intune, SCCM, Windows, Cloud PC, Entra, and Microsoft Security.
PakarPBN
A Private Blog Network (PBN) is a collection of websites that are controlled by a single individual or organization and used primarily to build backlinks to a “money site” in order to influence its ranking in search engines such as Google. The core idea behind a PBN is based on the importance of backlinks in Google’s ranking algorithm. Since Google views backlinks as signals of authority and trust, some website owners attempt to artificially create these signals through a controlled network of sites.
In a typical PBN setup, the owner acquires expired or aged domains that already have existing authority, backlinks, and history. These domains are rebuilt with new content and hosted separately, often using different IP addresses, hosting providers, themes, and ownership details to make them appear unrelated. Within the content published on these sites, links are strategically placed that point to the main website the owner wants to rank higher. By doing this, the owner attempts to pass link equity (also known as “link juice”) from the PBN sites to the target website.
The purpose of a PBN is to give the impression that the target website is naturally earning links from multiple independent sources. If done effectively, this can temporarily improve keyword rankings, increase organic visibility, and drive more traffic from search results.