Hey, let’s discuss about Sysmon Built into Windows for Easy Setup and Better Threat Detection. Windows 11 and Windows Servingr 2025 now includes Sysmon as a built-in feature. This eliminates the need to do so download or install that’s manually. It provides fast threat visibility with the same strong monitoring as previously. This update helps reduce work and improve
Built-in Sysmon sends events directly to the Windows event log and works well with SIEM tools. You can still use custom configuration files to control which events you want to collect. Monthly Windows Update keep Sysmon repaired and updated automatically. This lowers the risk outdated version and save time.
ysmon helps detect suspicious processnetwork connections, file activity, and credential theft attempts. Important events such as the Creation Process and Network Connection helps uncover offensive behavior early. These signals help uncover hidden malware or unusual traffic. Security teams can use it to investigate incidents more quickly.
You can activate Sysmon via Windows Features and a simple command: sysmon -i. Once enabled, all events appear on Sysmon/Operations event record. These logs can be used directly with SIEM or analysis tools. This built-in capability provides strong safety data with little effort.
Sysmon Built into Windows for Easy Setup and Better Threat Detection
| Configuration Type | Information |
|---|---|
| Configuration.xml | Default configuration. Include events that are considered “interesting” and exclude events that are particularly noisy. |
| Just Exclude | Logs everything except the specified list of noisy exceptions. |
| Super Verbose/Research | Record all events that may occur. No filtering or exclusion is applied. |
| MDE Augmentation | Designed to run alongside Microsoft Defender for Endpoint (MDE) |
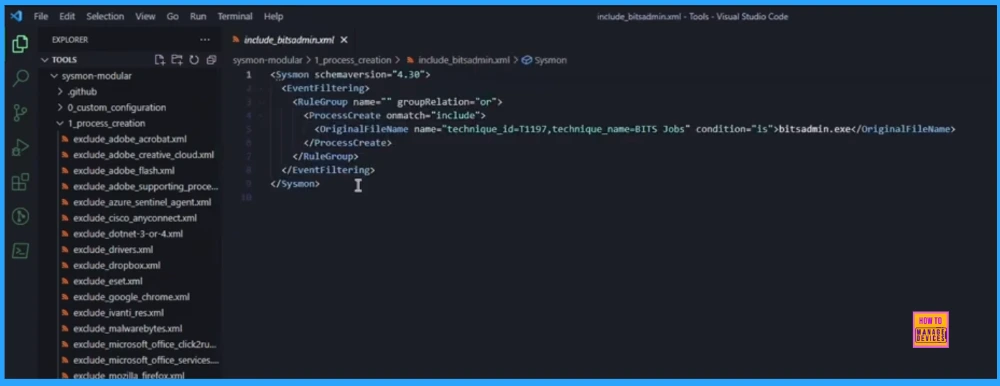
The screen switches to Visual Studio Code, showing the directory structure of the cloned repository. This view emphasizes modularitydisplays folders named after Sysmon events (e.g. ProcessCreate) containing many, smaller XML rules file.

The specific one XML file opened (ProcessCreate\Include_BitsAdmin.xml) to display the inclusion rules. The key visual element is an XML tag that explicitly references it MITER ATT&CK Engineering ID (T1197) first marked the event.
Complete XML Sysmon configuration file for the custom rule they just added (wind socks). The visual confirms that the new rules have been correctly entered into large configuration file.

The final custom configuration is updated successfully at the command prompt. The view then shifts to Windows Event Viewer, which immediately showed detailed new Sysmon log spikes (Image Loading, Process Access events) proving the point new rambling active rule.

Author
Anoop C Nair has been a Microsoft MVP from 2015 onwards for 10 years in a row! He is a Workplace Solutions Architect with over 22+ years of experience in the Workplace technology space. He is also a Blogger, Speaker, and Local User Group Community leader. The main focus is on Device Management technologies such as SCCM and Intune. He writes about technologies like Intune, SCCM, Windows, Cloud PC, Windows, Entra, Microsoft Security, Career, etc.
Game Center
Game News
Review Film
Berita Olahraga
Lowongan Kerja
Berita Terkini
Berita Terbaru
Berita Teknologi
Seputar Teknologi
Berita Politik
Resep Masakan
Pendidikan
Berita Terkini
Berita Terkini
Berita Terkini
review anime
Gaming Center
Originally posted 2025-11-21 16:07:03.