Key Points:
- Boot-Start Driver Initialization Helps reduce risks malware
- This is just making sure trusted driver loaded, strengthening endpoint security
- Prevent crime or unauthorized driver from loading on boot.
- Increase toughness against rootkits
Let’s discuss Enable Boot-Start Driver Initialization Policy to Reduce the Impact of malware on the System using Intune. This policy controls which drivers are allowed to load during booting Windows process. This security feature enables antimalware drivers (such as Microsoft Defender WdBoot.sys) to start before other third party drivers.
List of contents
Enable Boot-Start Driver Initialization Policy to Reduce the Impact of malware on Systems using Intune
By possible this and the organization of the settings ensure that drivers are blocked before they can even touch the kernel. Threat actors use malicious drivers to maintain access to a computer even after rebooting. This policy breaks that persistence by refusing to load drivers in next boot.
How to Start Policy Making
As AdminYou can quickly configure this policy in your organization. To start Policy Creation, go to Microsoft Intune Admin Center. Then go to Devices > Configuration >+ Create > +New Policy.
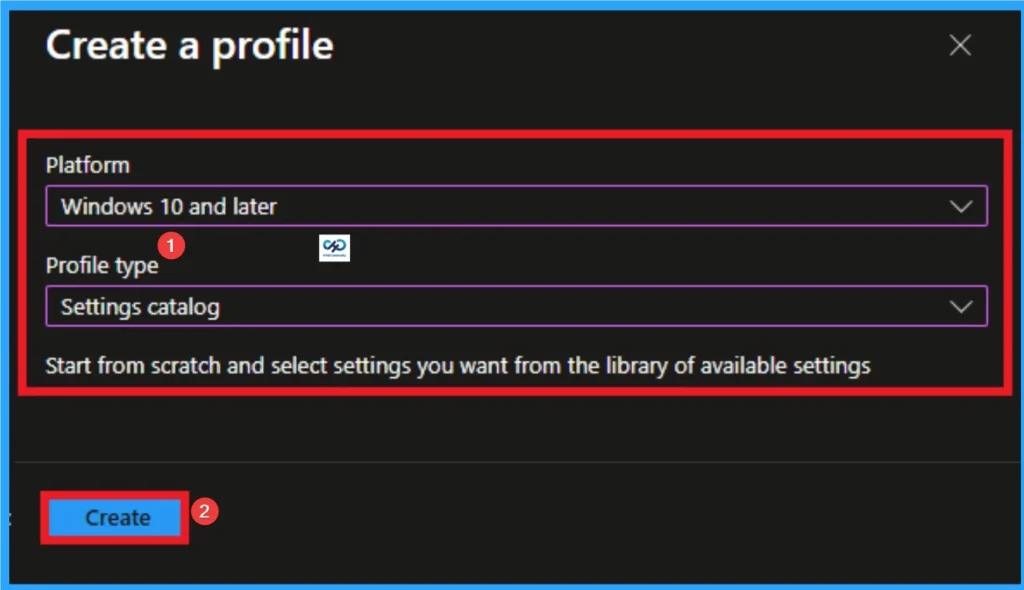
Profile Creation
Profile creation is an important step that helps you assign policies to appropriate platforms and Profiles. Here I want to configure the policy to be Windows 10 and laterr platforms and settings catalogue profile. Then click on Make knob.

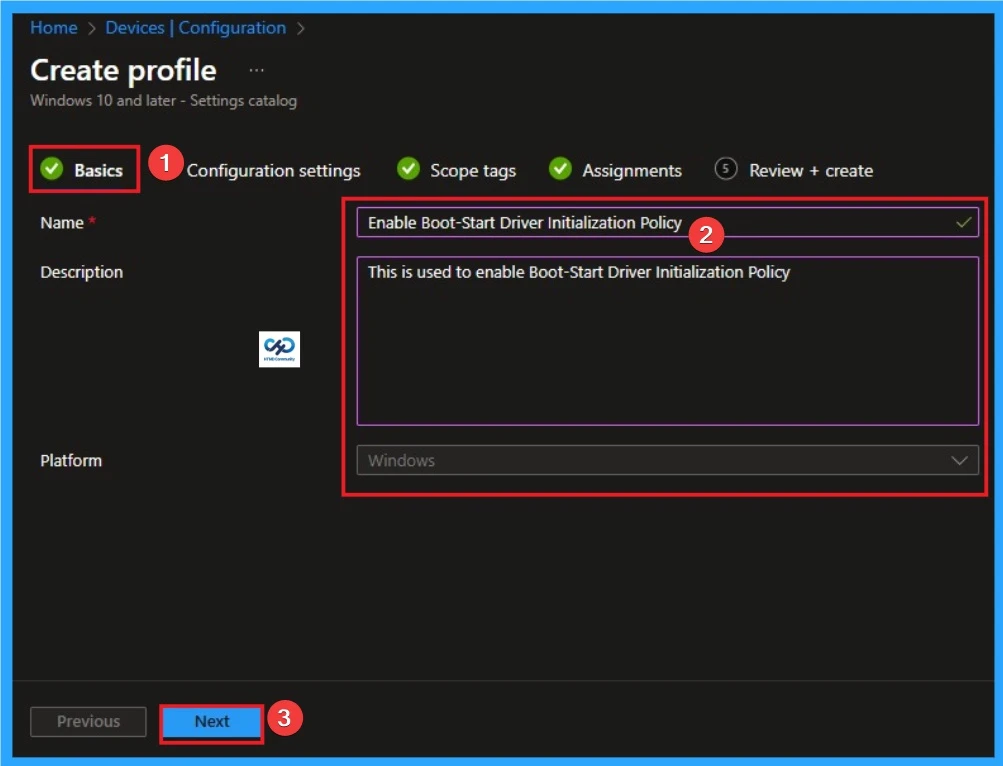
Filling in the Basic Tab
The name of the policy is main step which helps admin to identify policies later. This is an important and necessary step that allows you to know the purpose of the policy. This is his name must and description is optional. After adding this click on Next knob.
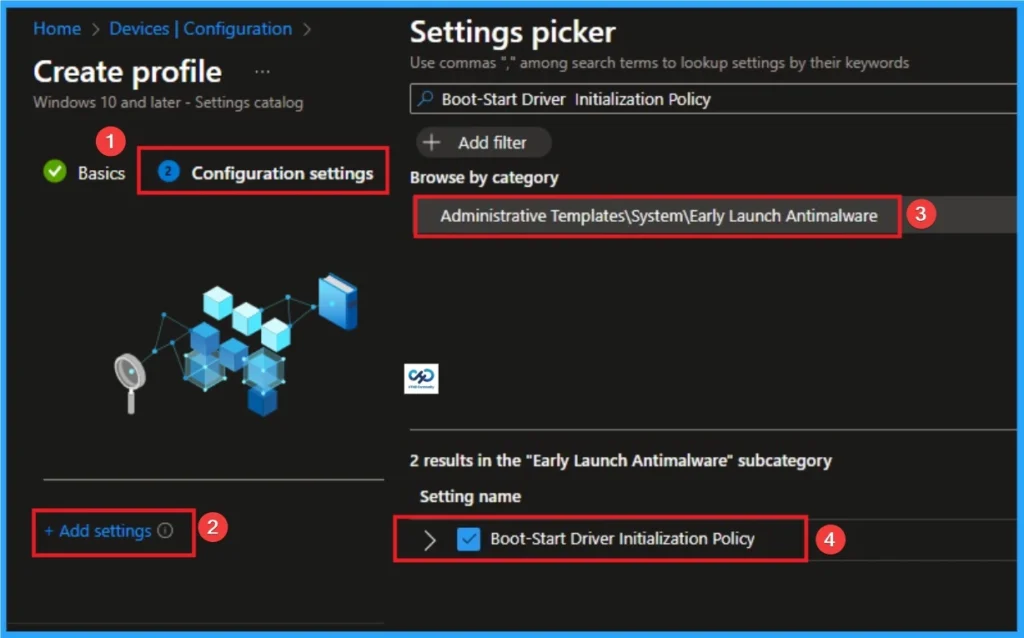
Configure Boot-Start Driver Initialization
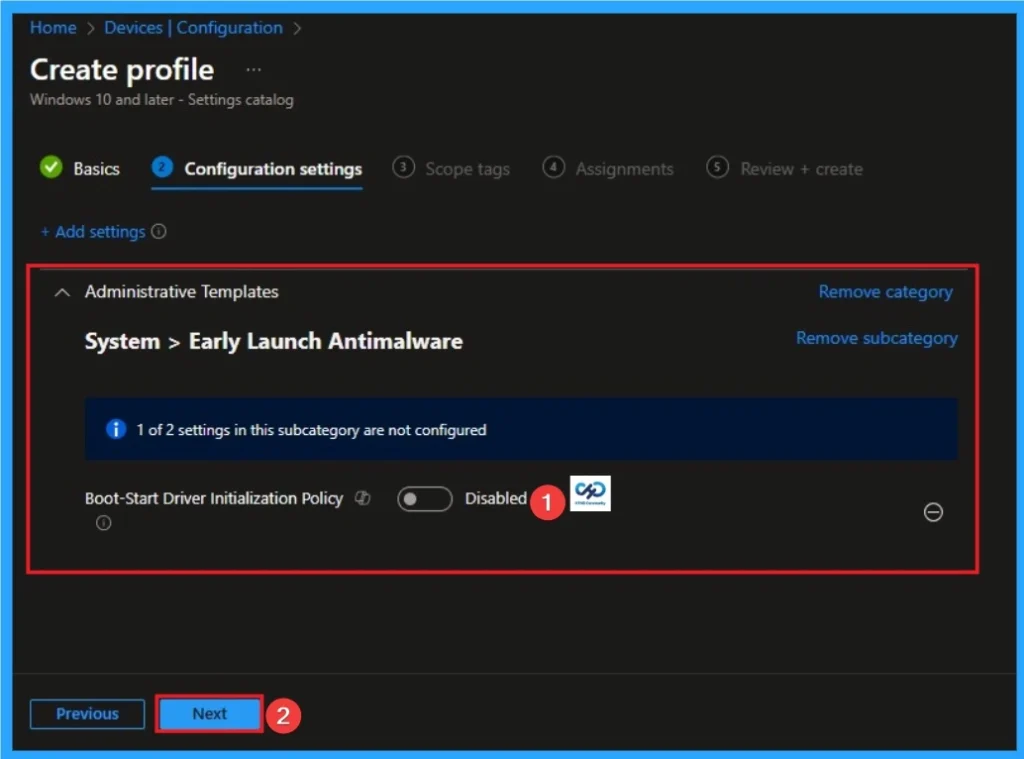
With Settings Picker, you can use the Configuration Settings Tab. In this tab, you can click +Add Settings hyperlink to get the Settings Selector. The settings selector shows a large number of settings. Here, I want to select settings by browsing by Category. I choose AAdministrative Templates > System > Antimalware Initial Launch > Select initializable boot-start drivers > Boot-Start Driver Initialization Policy Settings.
Disable Boot-Start Driver Initialization Policy
If you disabled or do not configure this policy setting, the boot start driver is determined to be Good, Unknown, or Bad but Critical Boot initialized and initialization of the specified driver Bad is skipped.
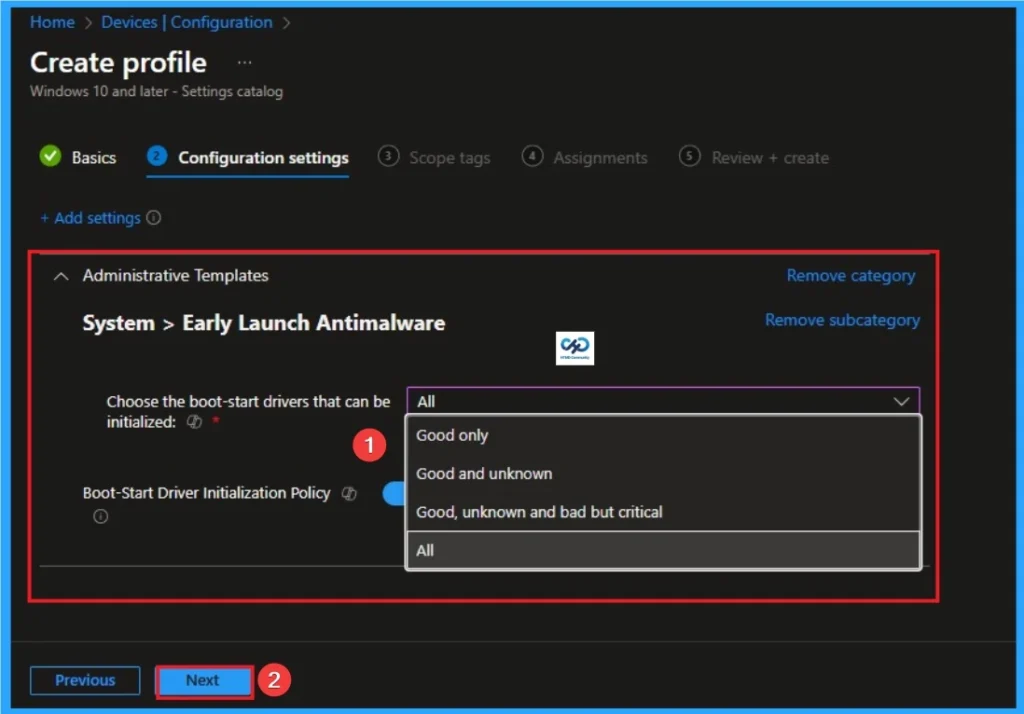
Enable Boot-Start Driver Initialization Policy
If you activate tWith its policy settings, you will be able to choose which boot-start drivers will be initialized the next time the computer starts up. There is Good, Bad, Good, but required to boot and Unknown. You can select one of these options and then click Next button to continue.
| Mark | Information |
|---|---|
| Good | That driver has been signed and has not been tampered with. |
| Bad | The driver has been identified as malware. It is recommended that you do not allow driver initializers that are known to be bad. |
| Bad, but necessary to boot | The driver has been identified as malwarebut the computer does not boot successfully without loading this driver. |
| Unknown | This driver has not been proven by your malware detection application and has not been classified by the Early Launch Antimalware boot-start driver. |
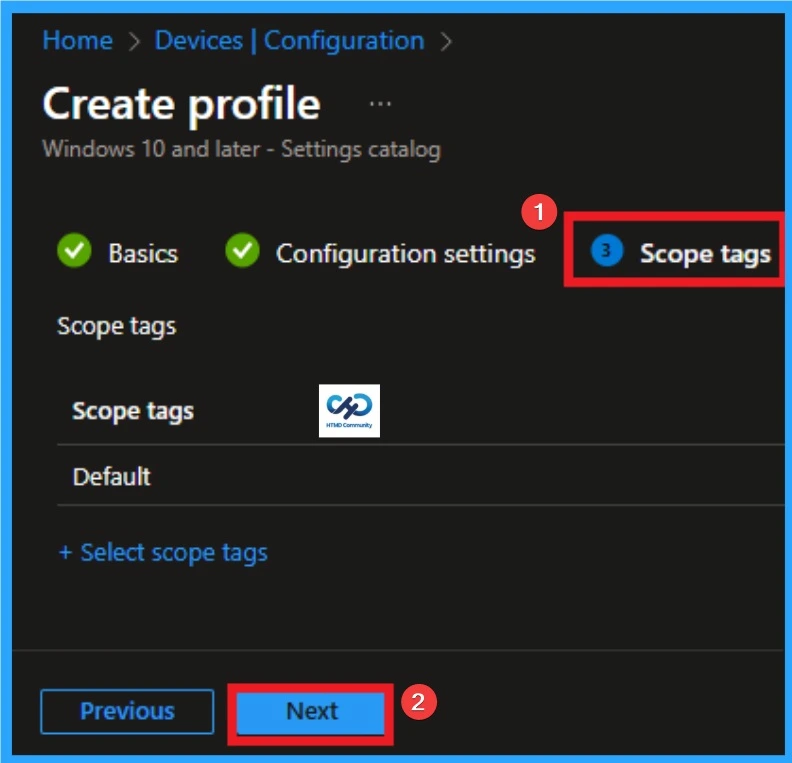
With scope tagYou create limitations on visibility Boot-Start Driver Initialization. This helps organize resources too. Here I want to skip this part because it is not mandatory. Click on Next knob
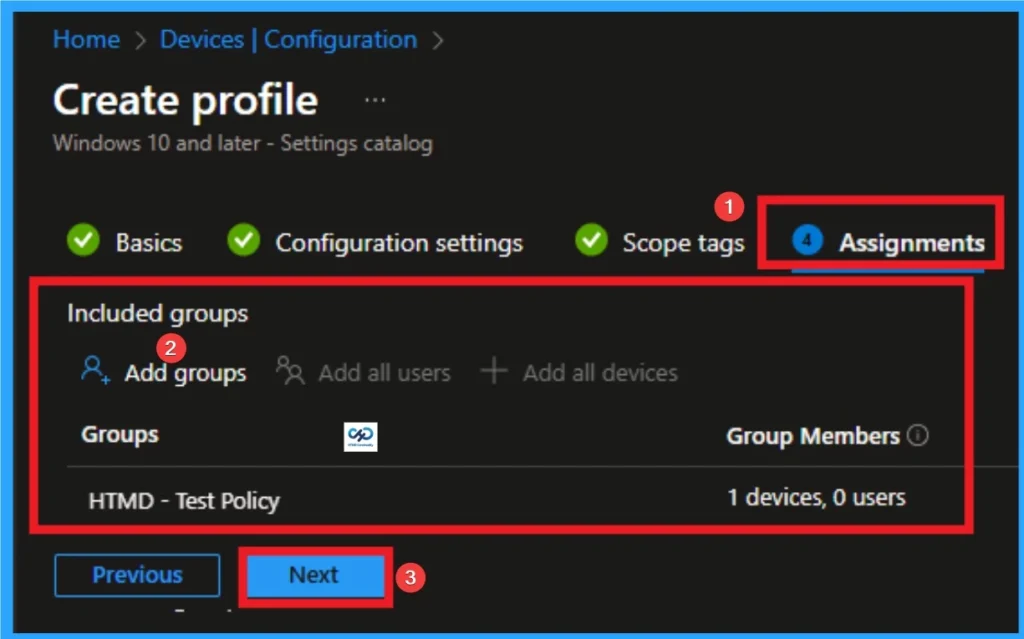
Tasks Tab for Selecting Groups
To assign policies to specific groups, you can use Tasks Tab. Here I click, +Add group option under Included groups. I select a group from the group list and click Choose knob. Again, I click on Choose button to continue.
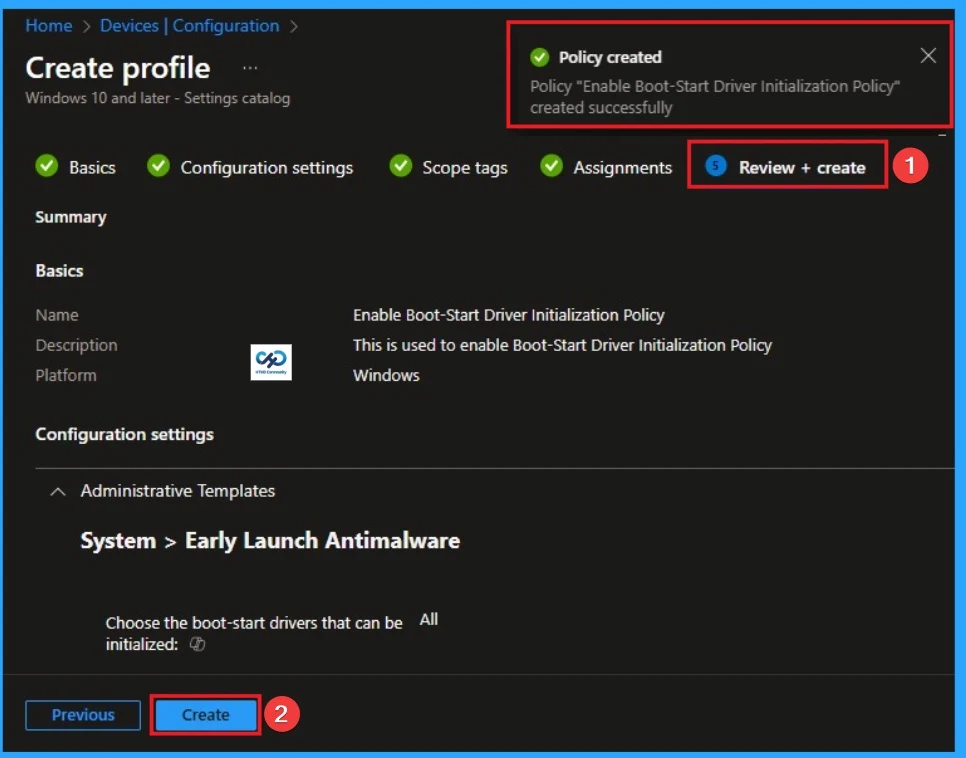
Review + Create Tab
Before completing policy creation, you can review each tab to avoid misconfiguration or policy failure. After verifying all the details, click Make Knob. After creating the policy, you will get a success message.
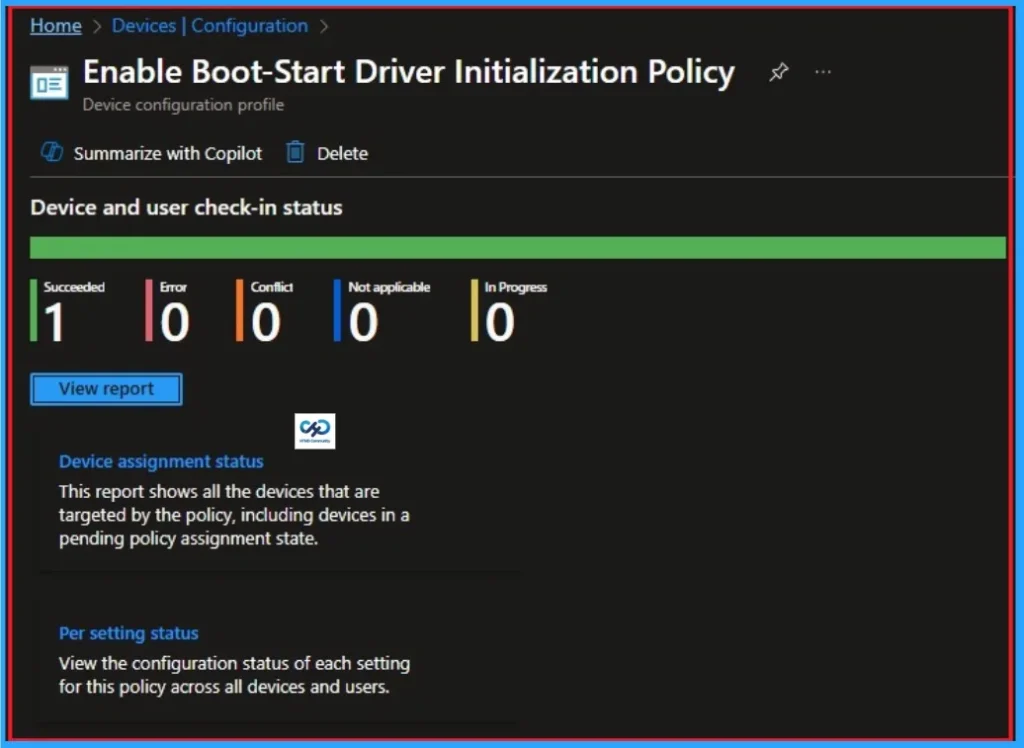
Monitoring Status
That Monitoring Status the page shows whether the policy was successful or not. To quickly configure policies and take advantage of them, sync the assigned devices in the Enterprise Portal. Open the Intune Portal. Go to Devices > Configuration > Search Policies. Here, the policy is shown as success.
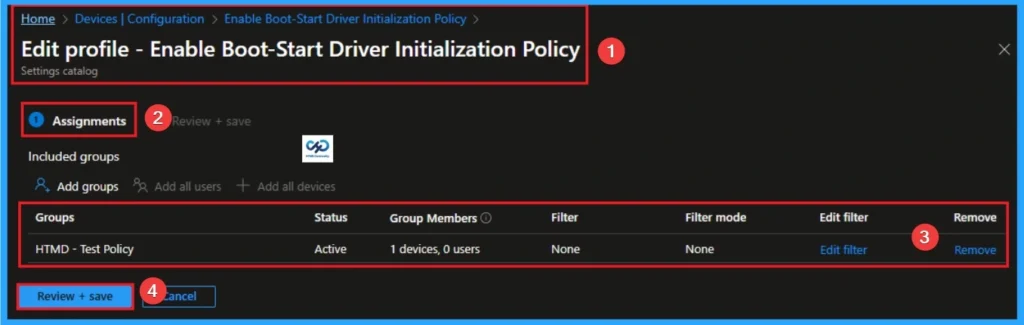
Delete an Assigned Group from Boot-Start Driver Initialization Arrangement
If you want to delete Assigned group from policy, can be from the Intune Portal. To do this, go to Policies in the Intune Portal and edit Tasks tab and Delete Policy.
To get more detailed information, you can refer to our previous post – Learn How to Delete or Unassign Apps from Intune using Step by Step Guide.
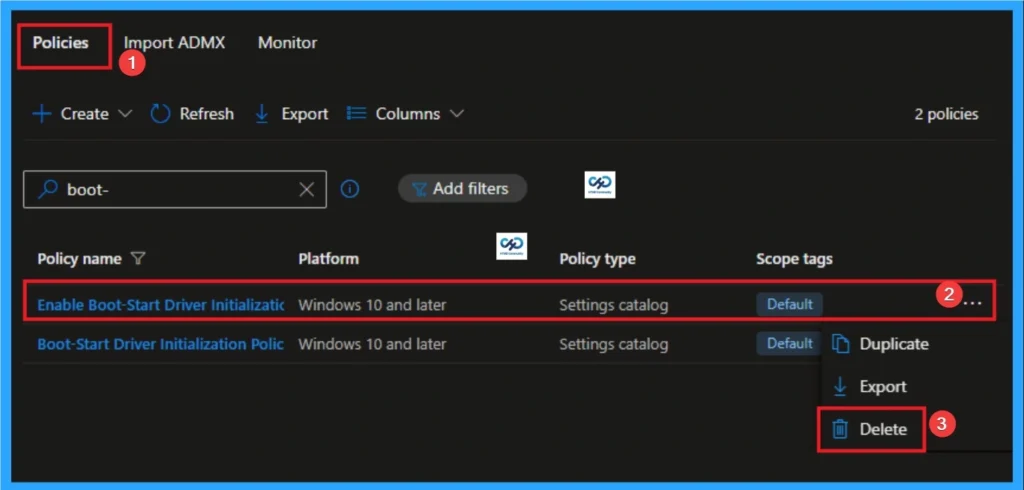
How to Delete Boot-Start Driver Initialization
You can easily delete Policies from Intun Portal. From Configuration section, you can delete the policy. This will remove it completely from the client device.
For more information, you can refer to our previous post – How to Remove Allow Clipboard History Policy in Intune Step by Step Guide.
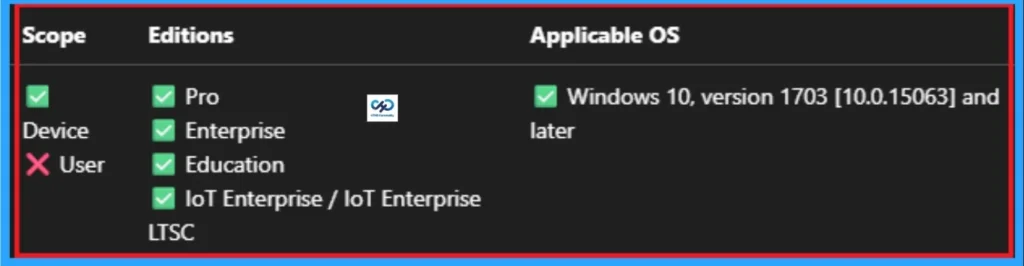
Windows CSP details
This policy setting allows you to determine which boot-start driver initialized based on the classification determined by the Antimalware Early Launch boot-start driver. That Initial Launch of Antimalware boot-start driver can return the following classification for each boot-start driver.
Need More Help or Have a Technical Question?
Join LinkedIn Page AndTelegram Group to get step by step guides and news updates. Join usMeeting Pageto participate in User group meetings. Also, JoinWhatsApp CommunityAndWhatsApp Channelto get the latest news about Microsoft Technologies. We were thereredditas well.
Author
Anoop C Nairhas been a Microsoft MVP for 10 consecutive years from 2015 onwards. He is a Workplace Solutions Architect with over 22+ years of experience in the Workplace technology space. He is a leader of the Community of Bloggers, Speakers, and Local User Groups. The main focus is on Device Management technologies such as SCCM and Intune. He writes about technologies like Intune, SCCM, Windows, Cloud PC, Windows, Entra, Microsoft Security, Career, etc.
News
Berita Teknologi
Berita Olahraga
Sports news
sports
Motivation
football prediction
technology
Berita Technologi
Berita Terkini
Tempat Wisata
News Flash
Football
Gaming
Game News
Gamers
Jasa Artikel
Jasa Backlink
Agen234
Agen234
Agen234
Resep
Cek Ongkir Cargo
Download Film