Block Executables that Emulate or Copy System Tools and Binaries using Intune ASR Rules. “Block executables that imitate or are copies of system tools and binaries” ASR rules in Intune is a security policy that helps you stop malicious programs that try to act like trusted Windows system tools.
Your Windows computer has many important things system toolssuch as cmd.exe and powershell.exe. It is installed and secure. However, sometimes hackers create fake version of these tool files that appear identical but actually contain malicious code. For example, they might create a fake “PowerShell.exe” and use it to attack your computer.
These Intune ASR rules help you stop those fake files. It checks whether programs pretending to be system tools are real or not. If it’s a fake copy, the rules will block it runkeep your device safe. These ASR rules are very helpful for admins and IT organizations as they add extra layer of protection against advanced cyber attacks that are often difficult to detect.
For IT admins, this reduces risk malware spreads via fake system files. They don’t need to manually check each executable. Intune automatically blocks any programs pretend be a Windows tool. This saves time and preserves endpoints security consistent across all managed devices.
For organizations, that is strengthen overall security by preventing attackers from using trusted Windows utilities for malicious purposes. This rule helps maintain a cleana trusted environment where only genuine system files can run, safeguarding both device and company data is safe.
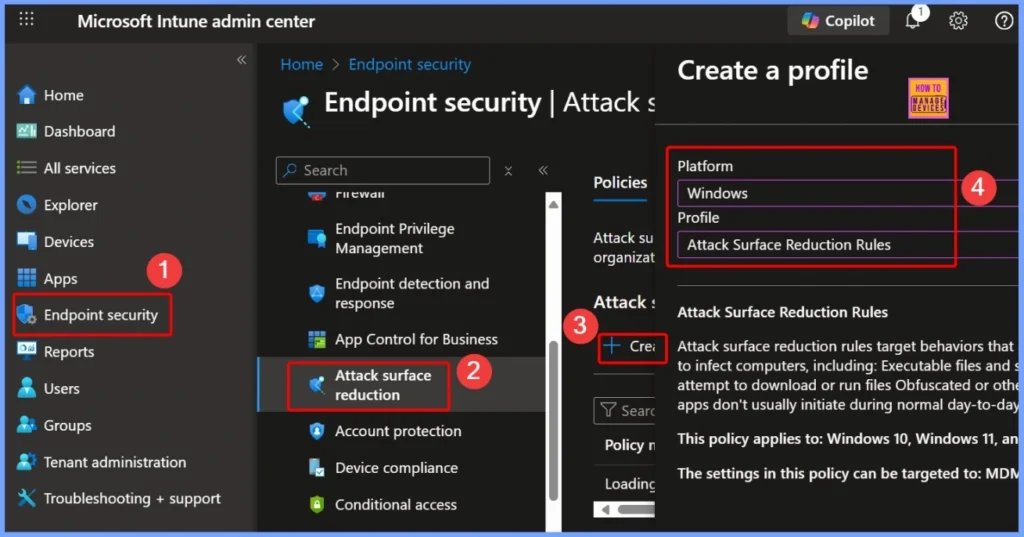
- To block use copied or imitated system tools, start by going to Microsoft Intune Admin Portal using your admin credentials.
- Once logged in, open it Endpoint security and select Attack surface reduction.
- From there, click Create a Policy to establish new ASR rules.
| Platforms | Profile |
|---|---|
| window | Attack Surface Reduction Rules |
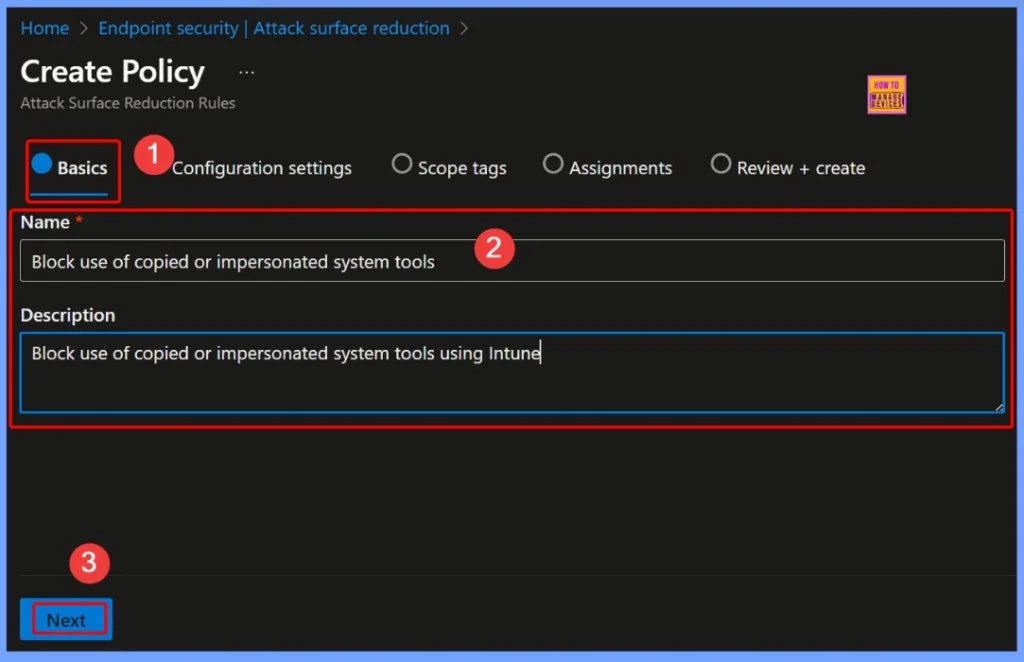
In Basics tab, provide the required details for your ASR policy. These details help clearly identify policy objectives in the Intune console. Giving meaning name and description makes it easy for IT admins to manage, track, and update rules as part of an organization’s endpoint protection strategy.
- Name: Block the use of copied or emulated system tools.
- Information: Block the use of copied or emulated system tools using Intune.
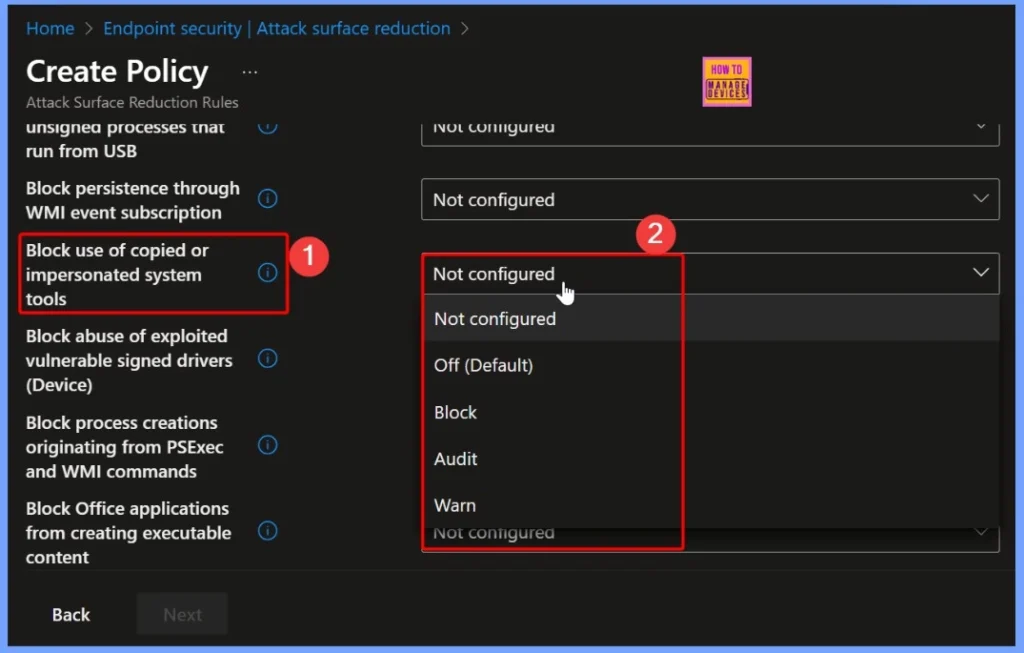
In this section, choose how the ASR rule should behave managed devices. You will see the following options available for configuration: To ensure maximum protectionselect Block, which prevents fraudulent or unauthorized copies of system tools from running on managed devices aligned.
| Policy Name | Available Options |
|---|---|
| Block Use of Copied or Emulated System Tools | Not Configured Off (Default) Block Auditing Warning |
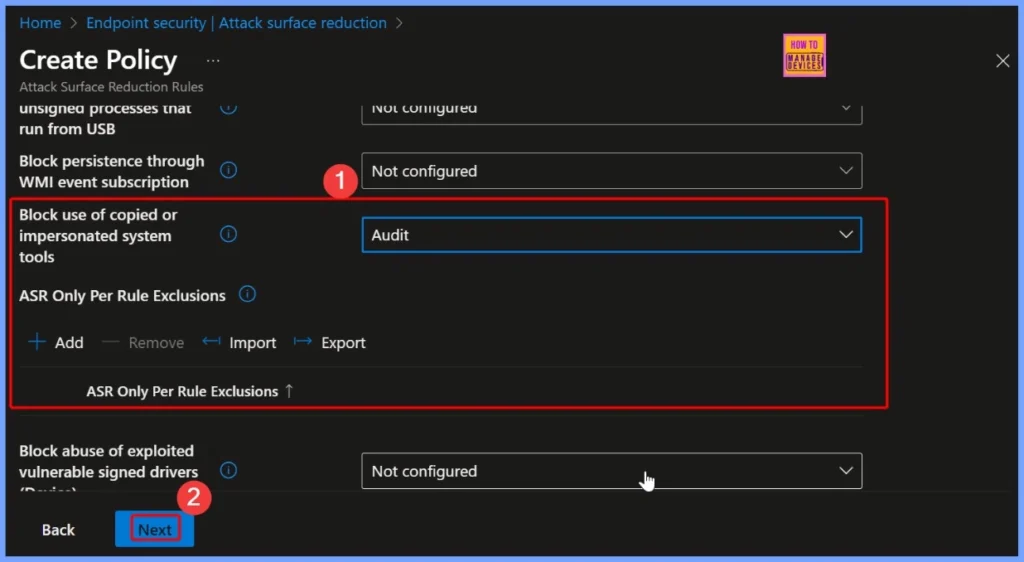
Set Policy to Audit Mode
In this policy, Auditing mode is selected to monitor the behavior of a rule before fully implementing it. When in audit mode, the policy does not block any executables, but rather blocks them notes all copied or imitated detection events system tools identified.
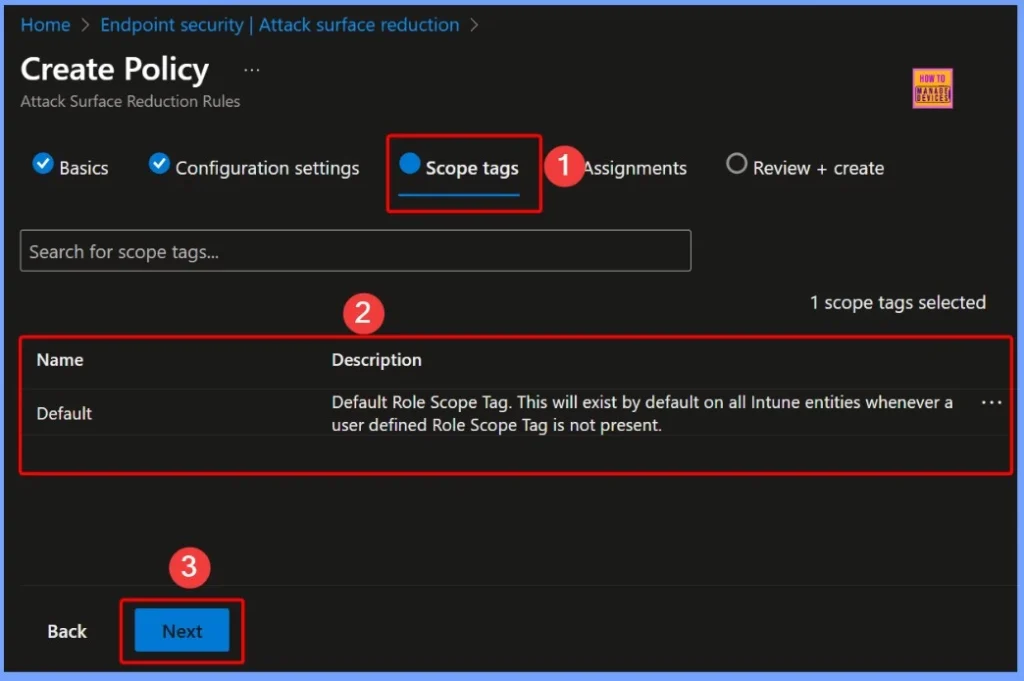
Coverage Tag – Default
That Scope Tag determine which admins or groups can view and manage specific policies in Intune. In this case, the default tag is named “Default” is applied automatically. This tag is used when no habits or a user-defined scope tag is set.
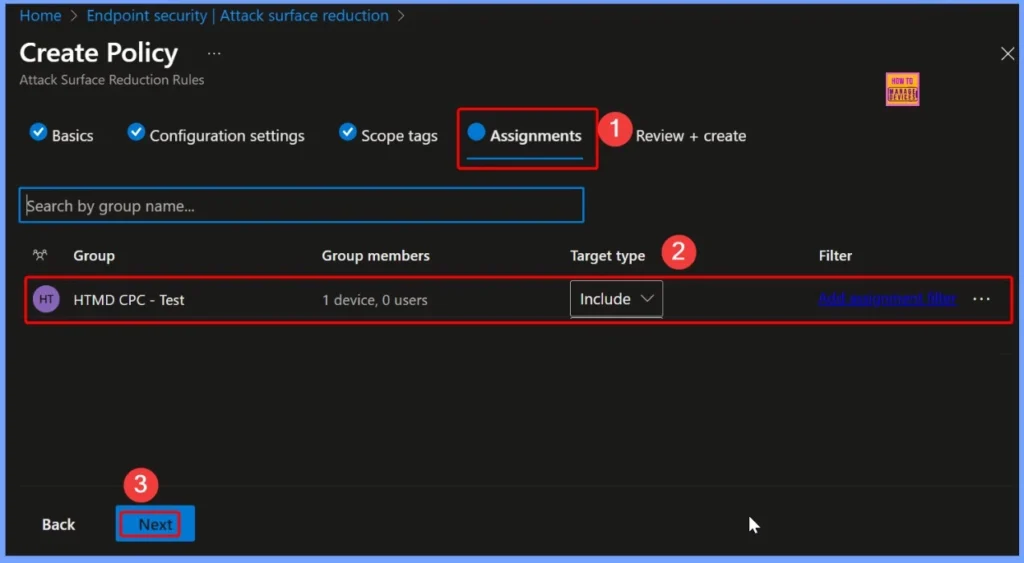
Assign Policies to Groups – HTMD CPC Test
In Task part of the policy, the target group of the HTMD CPC Test was selected. Assigning policies to these specific groups will ensure that ASR rules only applies to devices belonging to that group. This allows IT admins to test and monitor policy behavior in a controlled environment before it is implemented broadly throughout the organization.
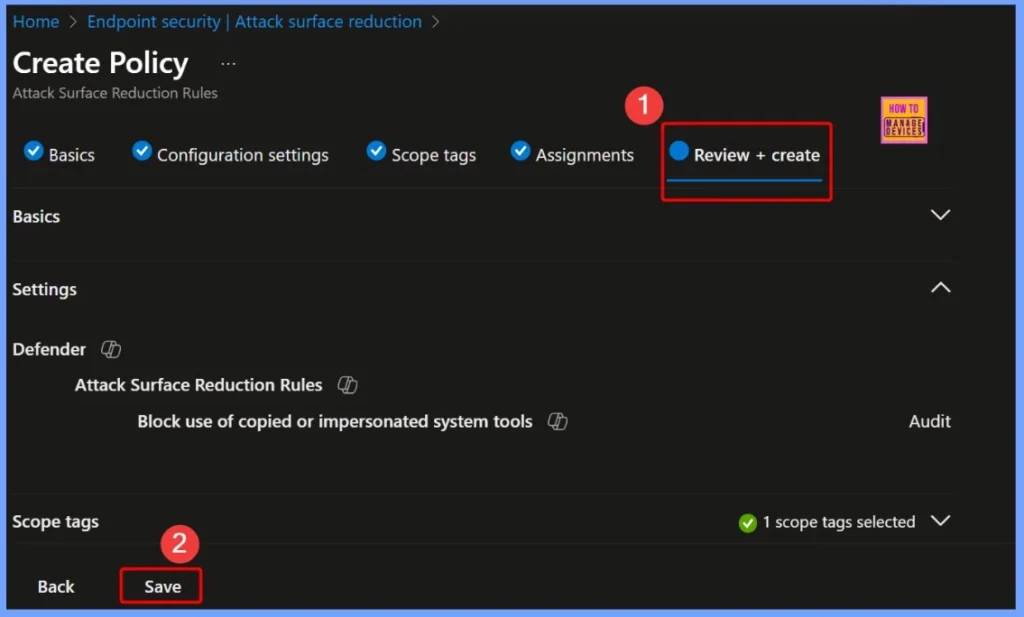
Review + Create Steps
This final step allows you to ensure that everything appropriate before implementation. Once you’ve reviewed and confirmed the details, click Make to finalize and implement the policy. The screenshot below helps you show more details.
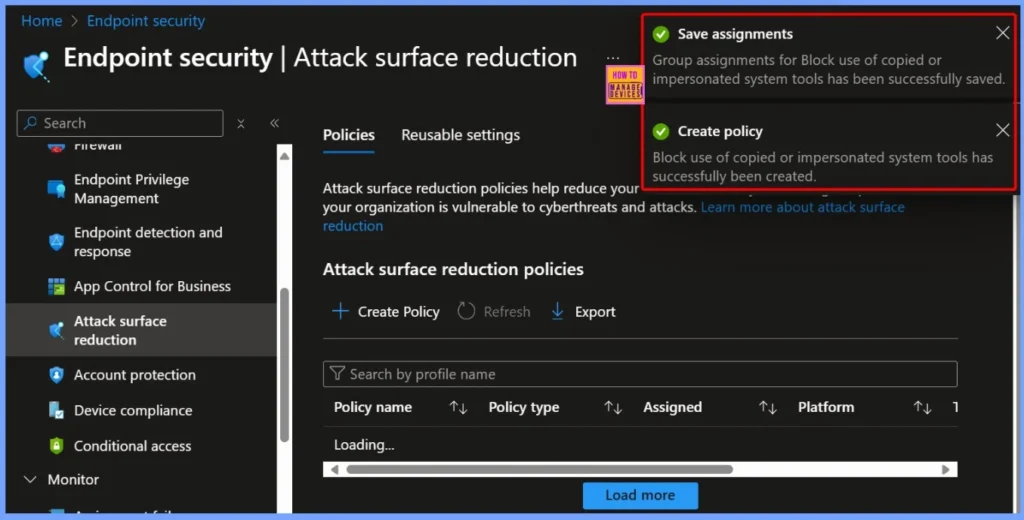
Policy Creation and Assignment Confirmation
After complete the settingsYou will see two confirmation notifications in the Intune portal. First message, “Create policies – Block use of copied or emulated system tools has been successfully created,” confirms that the policy has been successfully created. Second message, “Save the task – The group assignment for Block use of copied or emulated system tools has been saved successfully,” indicating that the policy has been correctly assigned to the selected group.
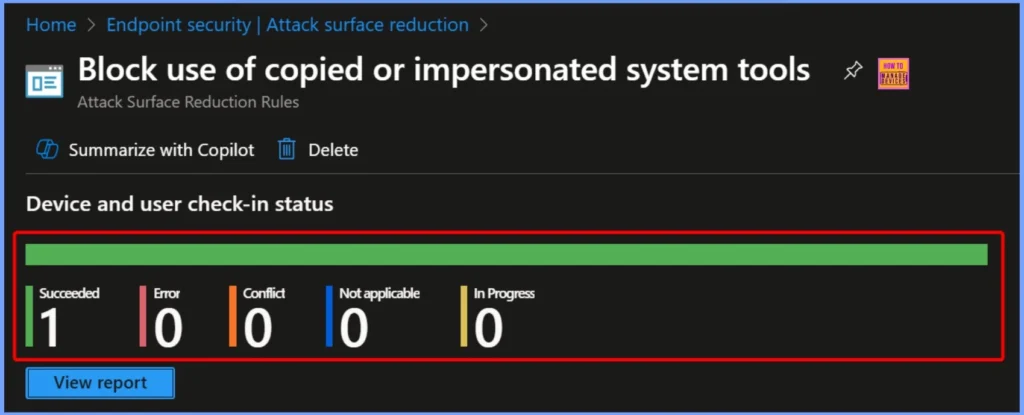
Device and User Check-In Status
After disseminate the policyDevices and Users Check-In Status shows the results of applying the policy across all targeted devices. Device and user check-in status are shown below.
- Success: 1
- Not applicable: 0
- In Progress: 0
- Errors: 0
- Conflicts: 0
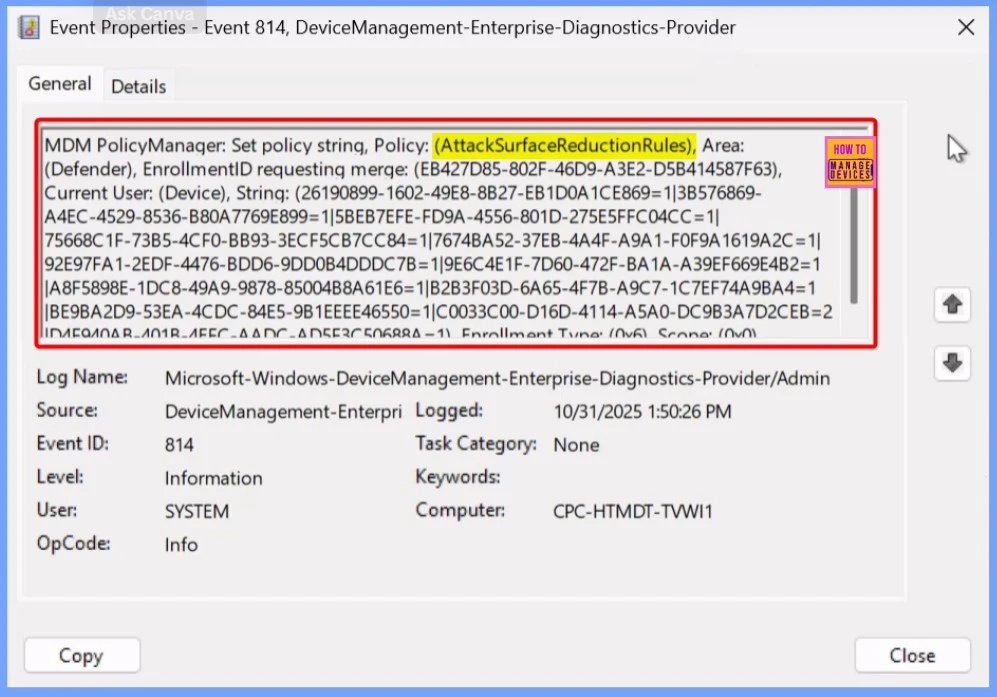
Verify Policy Enforcement in the Event Log
To confirm that the Block use of copied or emulated system tools policy has been successfully applied, you can check the device Event Viewer. Navigate to the following path: Application and Services Logs → Microsoft → Windows → DeviceManagement-Enterprise-Diagnostics-Provider → Admin
Need More Help or Have a Technical Question?
Join LinkedIn Page And Telegram Group to get step by step guides and latest news updates. Join us Meet Page to participate in User group meetings. Also, Join WhatsApp Community to get the latest news about Microsoft Technologies. We were there RepeatDhe as well
Author
Anoop C Nair has been a Microsoft MVP from 2015 onwards for 10 years in a row! He is a Workplace Solutions Architect with over 22+ years of experience in the Workplace technology space. He is also a Blogger, Speaker, and Local User Group Community leader. The main focus is on Device Management technologies such as SCCM and Intune. He writes about technologies like Intune, SCCM, Windows, Cloud PC, Windows, Entra, Microsoft Security, Career, etc.
Game Center
Game News
Review Film
Berita Olahraga
Lowongan Kerja
Berita Terkini
Berita Terbaru
Berita Teknologi
Seputar Teknologi
Berita Politik
Resep Masakan
Pendidikan
Berita Terkini
Berita Terkini
Berita Terkini
review anime
Gaming Center
Originally posted 2025-11-08 14:12:05.



