In this post we are discussing Reduced Security Risks with Restricting Anonymous Access Using Intune Policies. On a Windows computer, some system resources such as shared folders and named pipes are used to enable the computer and services convey one another. In the past, Windows allowed some of these resources to be accessed without a username or password.
This type of access is called anonymous or zero session access. Meanwhile useful previously, this was unsafe for today’s security requirements. Anonymous access can be misused by attackers to gather information from computers. Even without logging in, they may try to view shared resources or system details. This makes the system more open security threat.
Because of this risk, modern Windows system designed to limit what anonymous users can access. These security settings control how anonymous access works on the device. When did it happen activatedthe system allows anonymous users to access only specific sections and named pipes that are expressly permitted by administrator.
This helps the system follow a least access This approach only allows things that are necessary. This policy is important because it precludes methods commonly used by attacker to browse the network. Without anonymous access, it will be more difficult for them to find user accounts, services, or shared folders. It’s this simple restrictions adding additional layers protection without affecting normal users.

Reduce Security Risks by Restricting Anonymous Access Using Intune Policies
The settings work quietly on background by applying system-level rules. This uses built-in Window control which ensures the restrictions remain active even afterward restarted. Since this behavior is already the default in modern versions of Windows, possible it does not interfere with normal work or applications.
For organizations, this policy helps retain system safer and employees continue to work as usual, while the system is automated block unnecessary anonymous connection.
Create a Profile
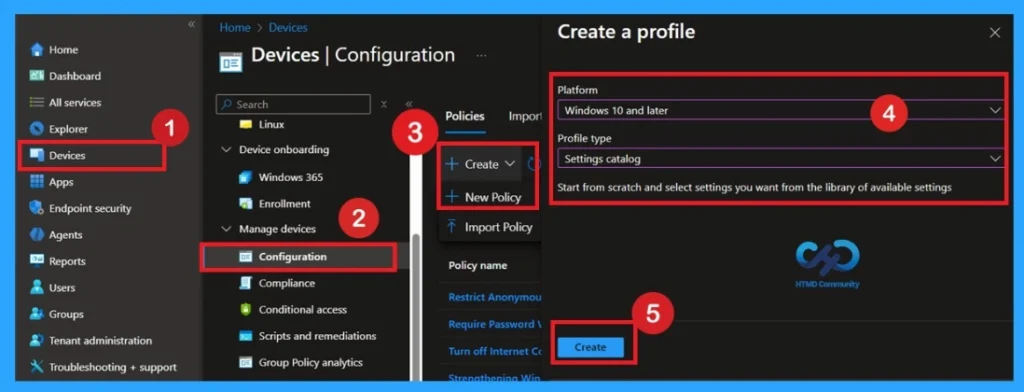
Now, let’s see how this policy can be implemented through Microsoft Intune Admin Center. First, go to the Devices section. In Devices, select Configuration. In Configuration, click the + Create policy option. Next, fill it in Platforms And Profile type details in Make profile window.
- Set Platform to Windows 10 and later and set Profile type to Settings catalogue.
- Then click Make.
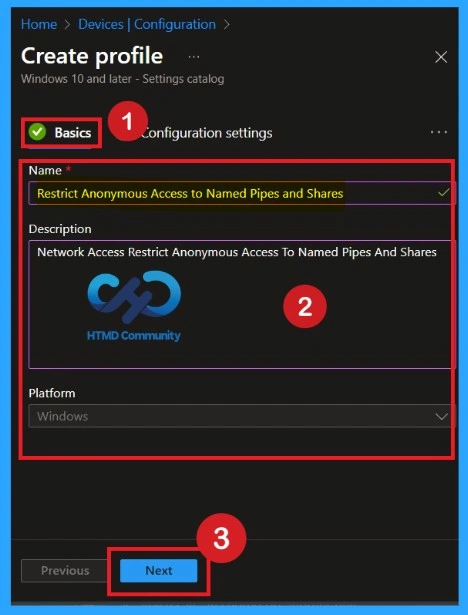
What are the Basics
Basic Details are very important here you have to include basic details like name and description. The description is must, but you can enter a description to understand the policy later. The platform has been selected as window so you don’t need to do anything.
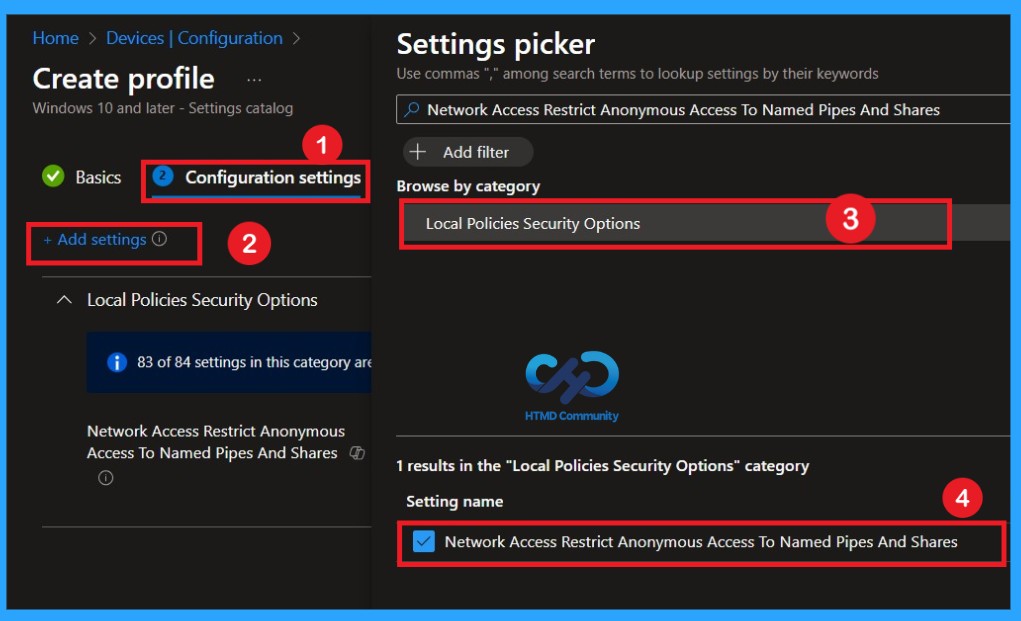
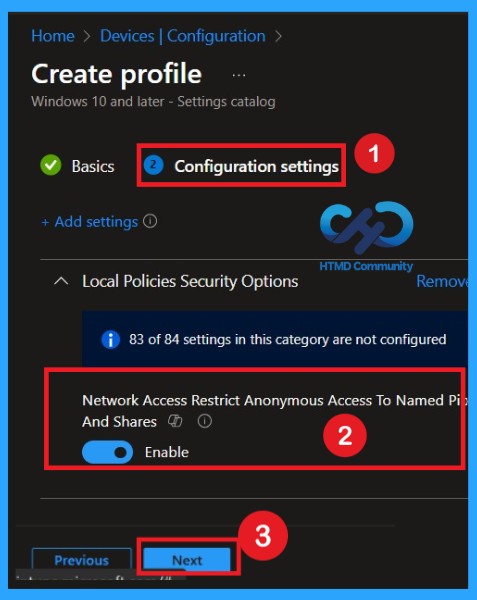
How to Handle the Configuration Settings Selector
Now, let’s see how to configure these settings in Settings selector. First, click Add settings. This opens the Settings selector window. In the search box, type Network access Restricts anonymous access to named pipes and shares. From the results, choose Local Policy Security Selected category. Then select the Network access policy: Restrict anonymous access to named pipes and shares. Once a policy is selected, close Settings selector window to return to the configuration page.
Disable Policy
By default, you should understand that a policy can be both activated or disabled. In this case, the policy is disabled by default. If you want to keep it in disabled mode, you have to click Next to continue.
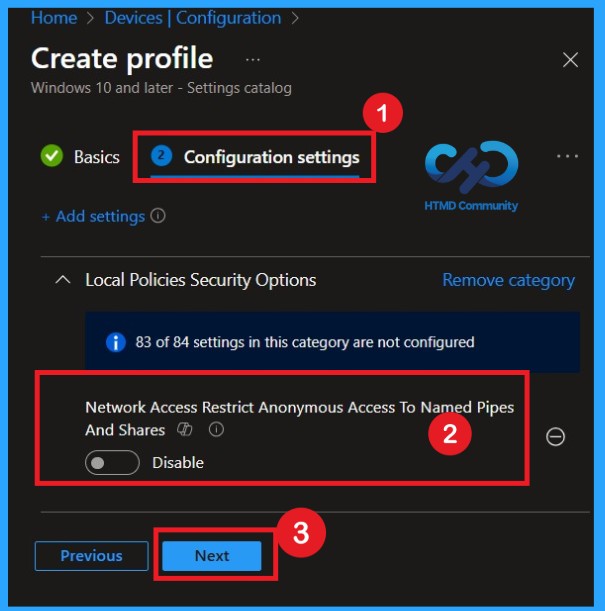
Enable Policy
The next and most important step is to activate the policy. This is very easy to do. By defaultpolicy is set to Disabled. To activate it, move it switch switch from left to right. After you do this, the policy status changes to Enabled, as recommended in CIS documentation.
- Enabling this policy helps create a safer environment.
- After enabling the setting, click Next to continue.
What is a Scope Tag
Now you are in the Coverage tags section. Coverage tag used to assign policies to specific admin groups for better management and filtering. If needed, you can add scope tags here. However, for this policy, I voted for it pass this part.

Importance of Task
Next, you will achieve Task section, which is a very important step. This is where you decide which user or device group must accept the policy. In this case, I choose certain groups I want to implement this policy. After selecting a group, click Next to continue.

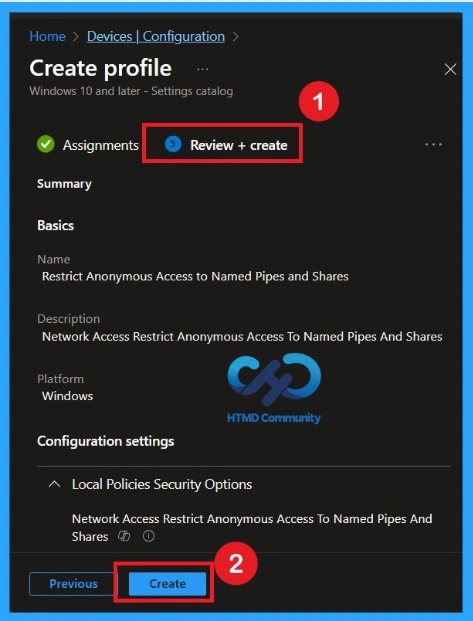
Review + Create
Review + Create is the final stage of policy making. In this step, you will see a summary of all the details, including Basics, Configuration Settings, Taskand much more. You can review them all informationand if anything needs to be changed, you can go back to the previous step and edit them easily. In Review + Create section, you will see a Create button.
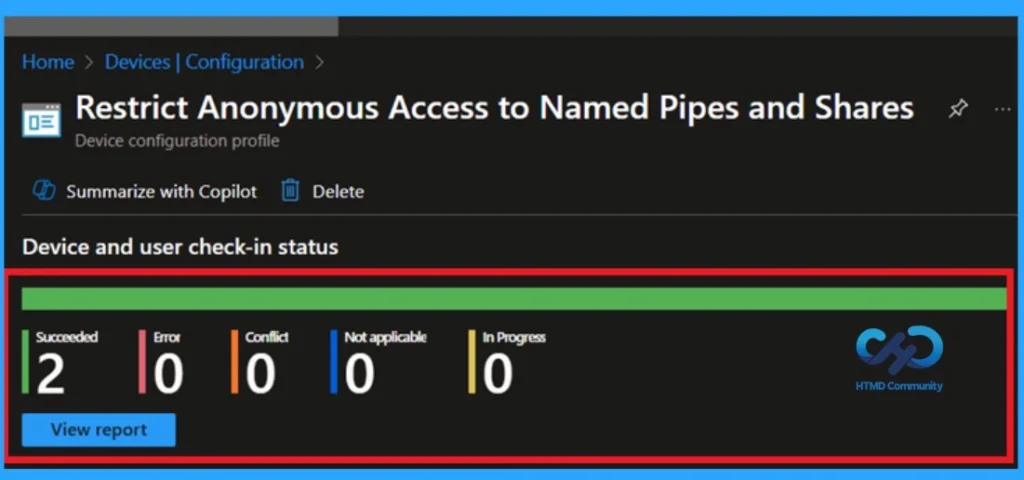
Monitoring Status
Once a policy is created, the main concern is whether the policy has been created deployed successfully. Typically, this can take up to 8 hours so that the policy can be implemented. This is the minimum amount waiting period. However, you can synchronize manually the policy through Company Portal, which helps implement policies more quickly. To check whether the policy has been successfully implemented.
- In Configuration Policy register, search for the policy you created.
- Click on a policy to view it spread status and details
- Sign in to Microsoft Intune Admin Center.
- Navigate to Device > Configuration Policy.
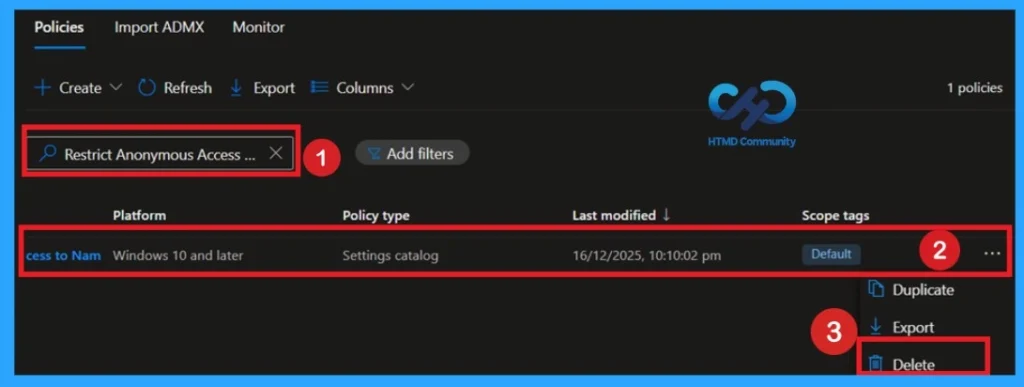
Delete Policy
To delete a policy in MS Intune, first log in to the Microsoft Intune Admin Center. Navigate to Device then select Configuration. Search for and select the specific policy you want delete. Once you are on the policy details page, click 3 dot menu in the top right corner and select Delete from the available options.
For more information, you can refer to our previous post – How to Remove Allow Clipboard History Policy in Intune Step by Step Guide.
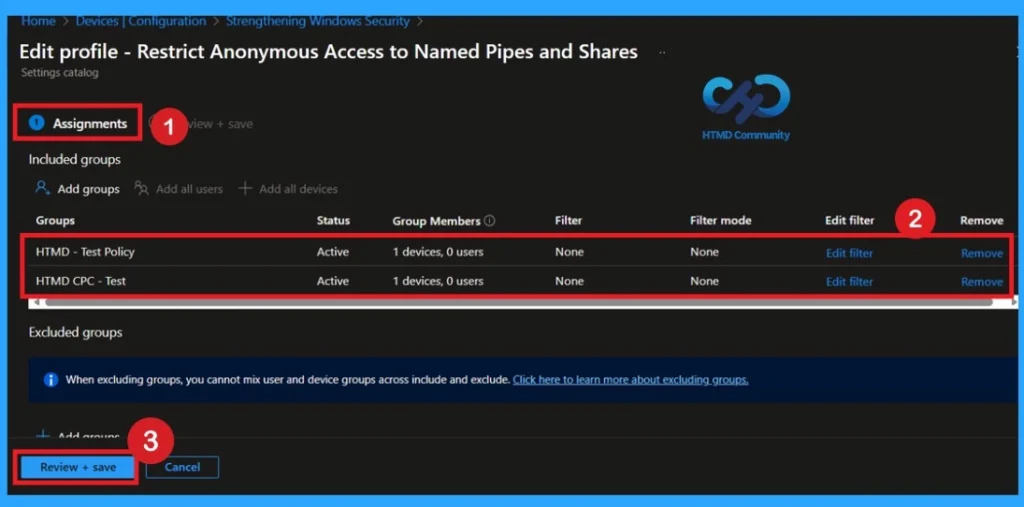
How to Delete a Policy Group
Start by navigating to the Monitoring status page via Device > Configuration. Browse a policy by name and click to open its monitoring details. Scroll down to the Tasks section and click Edit. This will take you back to the policy assignment arrangement.
- From here, you can delete groups whose policies you no longer want.
For more information, you can refer to our previous post – Learn How to Delete or Unassign Apps from Intune using Step by Step Guide.
Need More Help or Have a Technical Question?
JoinLinkedIn Page AndTelegram Groupto get step by step guides and latest news updates. Join usMeeting Pageto participate in User group meetings. Also, join inWhatsApp Communityto get the latest news about Microsoft Technologies. We were thereredditas well.
Author
Anoop C Nairhas been a Microsoft MVP for 10 consecutive years from 2015 onwards. He is a Workplace Solutions Architect with over 22+ years of experience in the Workplace technology space. He is a leader of the Community of Bloggers, Speakers, and Local User Groups. The main focus is on Device Management technologies such as SCCM and Intune. He writes about technologies like Intune, SCCM, Windows, Cloud PC, Windows, Entra, Microsoft Security, Career, etc.
News
Berita Teknologi
Berita Olahraga
Sports news
sports
Motivation
football prediction
technology
Berita Technologi
Berita Terkini
Tempat Wisata
News Flash
Football
Gaming
Game News
Gamers
Jasa Artikel
Jasa Backlink
Agen234
Agen234
Agen234
Resep
Cek Ongkir Cargo
Download Film



